(Guest post from Cybernews)
According to researchers at Ladders, 25% of professional jobs in North America will be remote by the end of 2022. Remote jobs skyrocketed from under 4% in 2019 to 9% in 2020 alone. This means that working from home is here to stay.
With this change in the job market demand, distributed teams have become more common and will continue to be adopted by small and big businesses alike. The need to secure company and employee data is important given the rise of internet scams. It is advisable to have all team members engage in security awareness training to have them prepared against malicious hackers and phishing sites.
Here are measures distributed teams can take to protect themselves and the company from a security breach.
Public Wi-Fi
Avoid using public Wi-Fi, especially from unknown service providers. If you must connect to a public server ensure you have a VPN installed on your computer to prevent hackers from monitoring your internet activity.
Social engineering
Social engineering uses manipulative techniques to gain confidential information that can put an individual or company at risk of cyber-attacks. Hackers have gotten smarter over time creating the need to be cautious mainly when workers use their own devices for office duties. Here are tips to save you from falling victim to such scams.
- Be suspicious if an unknown person asks you for information, they shouldn’t have access to it. All workers have team leaders they report to or team members that handle specific company data. If someone aside from the usual team member is asking for such data, be alarmed and report it to your team leader.
- Pay attention to emails. It can be daunting to always have to check an email sender to be sure you’re not under a phishing attack, but it can save you from putting your company at risk. Look out for grammatical errors and the sender’s email address to be sure they aren’t impersonating your company’s or an employee’s email.
- Beware of heightened urgency. Resist the rush to perform an action if you are feeling pressured to perform a certain action. Creating urgency is a common tool phishing scammers use to make their victims act fast. You should be more suspicious if the person is trying to make you ignore a mandatory security protocol.
- Always hover over links to see where they lead. Don’t be quick to click links and open attachments sent to you from new contacts. Offerings of things that are too good to be true are not true. An example is an email congratulating you on an iPhone in a competition you never attended.
- Never download unauthorised software or plug in an unauthorised drive or USB to your device.
Setting passwords
Most websites will tell you to create an 8-character password that contains uppercase letters, lowercase letters, numbers, and symbols that should be changed every 90 days. However, cybercriminals now use technology that allows them to crack an 8-character password in 4 hours. That’s why you should be using strong password management.
Instead, use a 12–16-character password with uppercase and lowercase letters, numbers, and special characters. You can create a passphrase using multiple small words like “tiNyTombSPoon.” Combining your passphrase with numbers and special characters is advisable for added difficulty. Complex passwords like this should be changed every two years.
Never save passwords to browsers. Never share your passwords with anyone or log in to your work accounts with public computers. Ensure you use a unique password for each account, you can use a password keeper if necessary.
Always use two-factor authentication for all your accounts. Never use the same passwords for your personal and work accounts. Make sure to separate your personal and work life.
Security awareness at home
In a world of distributed teams, it is normal for workers to spend more time at home than in an office. Here are measures that can be taken to stay safe when working from home.
- Never grant anyone access to your desktop unless you sort the remote connection. Always be careful of remote desktop inquiries. Never give out your login details to anyone over email or phone without consulting your supervisor.
- Don’t respond to non-company numbers or messages regarding an issue when you didn’t open a ticket.
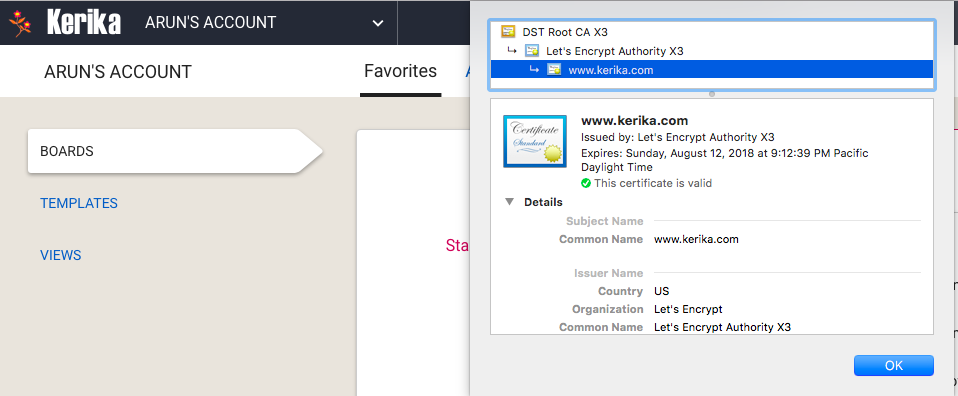
- If you will be filling your data into any websites while working, ensure they begin with https://
- Ensure your Wi-Fi router is secured with a strong password. Always restart your router frequently.
- Keep your working devices out of the reach of family and guests. Use a different internet network for work and family or guests.
- Only use company-approved USB sticks. Never use unencrypted USB sticks to connect or charge your work device in public places.
- Never leave your work device unattended. If you aren’t actively using your device ensure you exit your work screen and lock or close your device.
Security awareness in videoconferencing
All virtual meetings should be cyber-safe and not open to the public. Links to video meetings must not be shared on public sites. Ensure all meetings require passwords to join. Avoid starting a meeting without the host – rather create a meeting room.
Enable host-only sharing, accept one user at a time, and lock the meeting after all the participants are in.
Other security measures
- Avoid using your personal computer or smart devices for work. Ensure your operating system, antivirus and apps are updated frequently.
- Beware of phishing links sent to your email. Alert your family members on using your devices without your supervision.
- Beware of pop-ups on free movie sites and apps asking you to install software from unverified sources.
Conclusion
Although it is impossible to be 100% secure, raising awareness of the cybersecurity risks and taking all security measures stated above is key to preventing a security breach that can lead to catastrophic events. Ensure each team member is properly oriented on security measures to employ and things to look out for to prevent getting hacked.